What Is A Malware?
What Is A Malware? How Does Malware Work?
A Malware is a special type of program, designed to harm your machine. A Malware can steal data from your device or system. It can also hijack your device or system. There are different types of Malware:
Spyware:
A spyware is designed to spy your device or system and steal data from it. Spyware can steal your username and passwords from your computer or mobile. It is used to leak secret data to the hacker to make their work easier.
Adware:
And adware is designed to show ads on your device. By showing ads, the adware creator actually gets paid. It can be easily installed on an android phone and shows the user is irrelevant ads.
Rootkit:
Rootkit can gain access to the root of your device and install adware or other types of Malware to harm your device or to steal data from your device.
Viruses:
Viruses can also be described as malware. A virus can harm your device, leak sensitive information from your device like username and passwords and credit card details. That's why it is the most dangerous type of Malware.
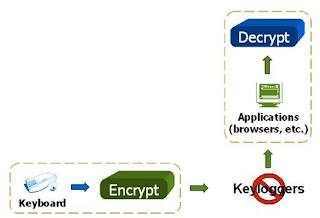
Keyloggers:
Keyloggers are one of the most dangerous types of Malware. A Keylogger records your keystrokes. It is used to sniff usernames and passwords from your device. Suppose you have a keylogger installed on your computer and you type your username and password in Gmail or Facebook or anywhere, what a keylogger does is, it records your keystrokes and sends it to someone else so that he can easily find out your usernames and passwords.
 |
| Malware |
How can a Malware get into your device:
Downloading software from unknown sources:
if you download any software from unknown sources then there is a chance that a Malware is bound with that software. installing that software the Malware also gets installed automatically. Many times Malware is installed by inserting a pen drive or CD drive into your device that is taken from unknown sources.
Sometimes visiting harmful websites can also install Malware into your device. Have you ever seen that visiting some mobile websites causes your phone to vibrate automatically and a warning pops up that your device is infected with viruses? That is an indication that your device can really get affected. Many times there is a download button there. If you click on the download button and let the app get downloaded (thinking that it is anti-virus), surely it is a virus, hernia device.
That's how Malware can affect your device and still sensitive information from it. Subscribe to this blog to get more updates about this topic and to stay secure from cyber threats.